WORMS, VIRUSES, and SCRIPTS 2
-Zhelatin worm: P1/P2
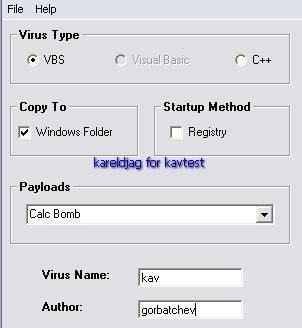
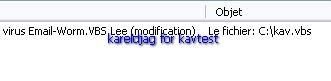
-"Kav Virus": P1/P2
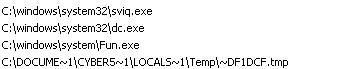
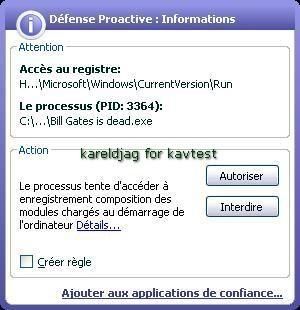
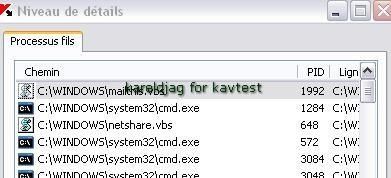
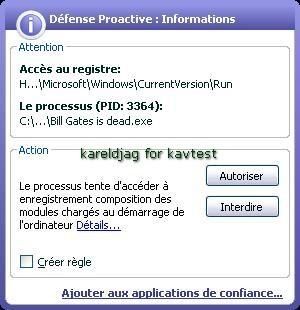
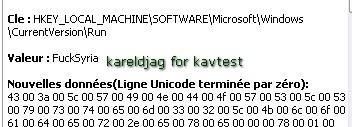
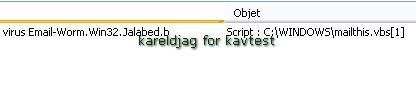
Here we just create a simple malicious scripts that we call "kav virus":


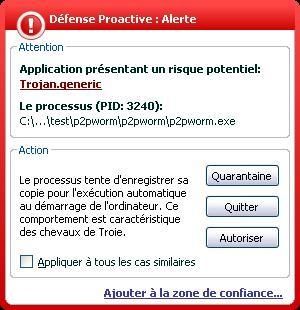
 -P2P-WORM.Win32.Small.y: P1/P2
-P2P-WORM.Win32.Small.y: P1/P2
-Worm.Win32.Agent.ak: P1/P2

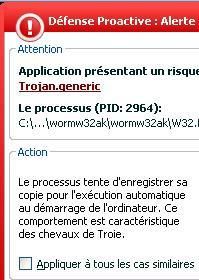
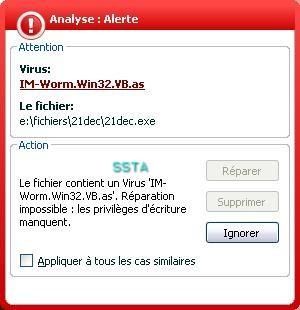
-IM Worm Win32.VB.as: P1/P2
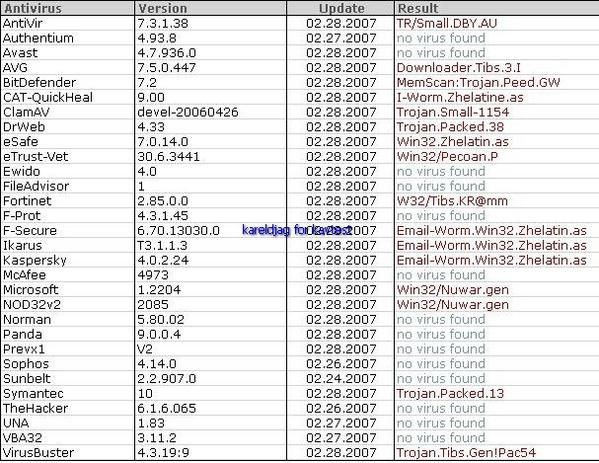
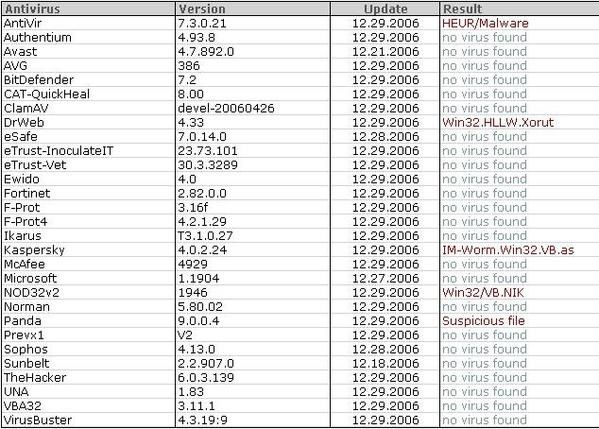
Scan for the first test ("fresh mawlare"):
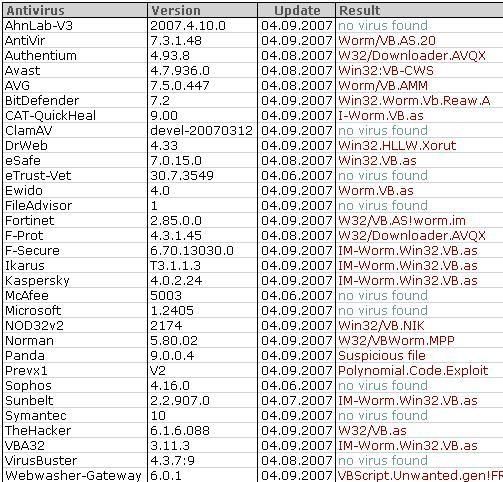
Scan for the verification test:
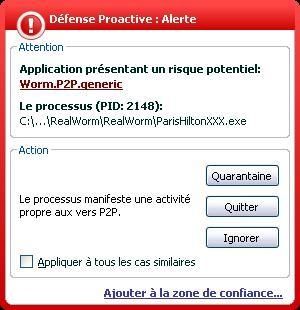
We have renamed the infection vector file as ParisHiltonXXX:

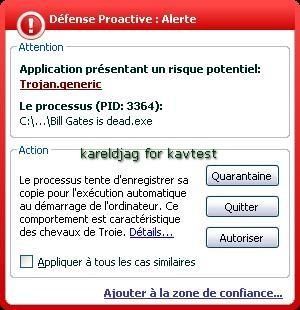
NB. More than really dangerous, this malware is a real annoyance which has infected our USB key (we have saved test results and screenshot in a folder that we had copied on the USB key).
We needed to erase each copied and infected folder manually...
And for the CDRom, the AV is really useful to locate every replicated folder:


-Worm Win32.Saros: P1/P2

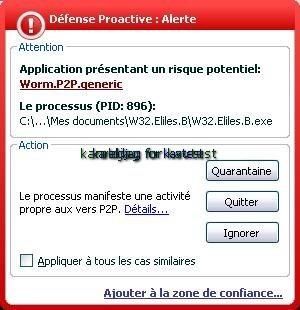
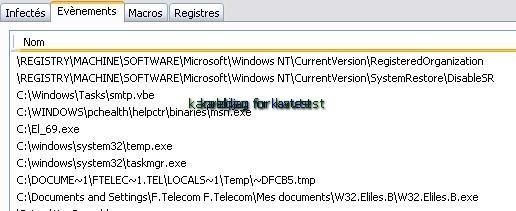
-P2P Worm Win32.Elies.b: P1/P2
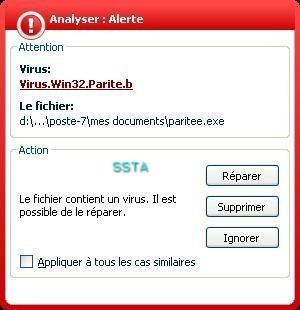
-Virus Win32.Parite.b: P1/P2